Age Verification Systems Face Encryption and Circumvention Challenges
Proposed age verification frameworks for online platforms confront technical obstacles as security researchers highlight encryption methods and decentralized alternatives that make comprehensive enforcement difficult.
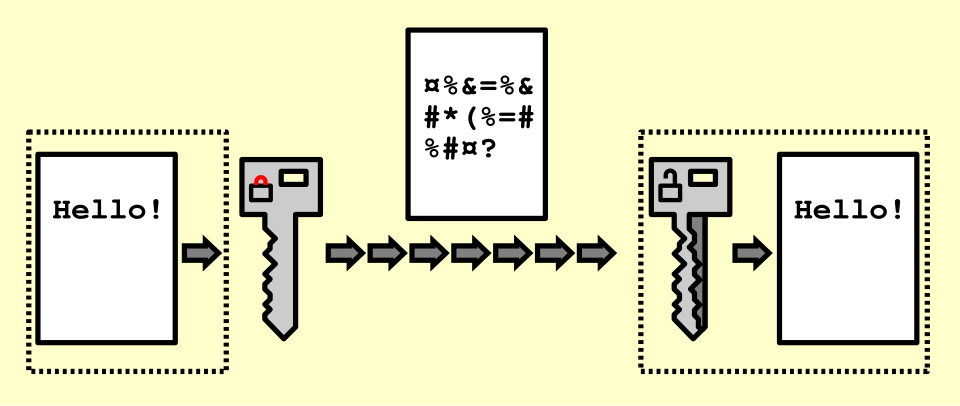
Governments and technology companies worldwide are advancing age verification systems to restrict minors from adult content, but technical experts say the initiatives face significant hurdles from encryption, traffic obfuscation, and decentralized alternatives.
The push for mandatory age verification has accelerated in recent years, with major technology firms investing billions in identity-verification infrastructure. However, the approach has sparked debate among security researchers and privacy advocates who argue that comprehensive enforcement remains technically infeasible.
“Encryption and obfuscation present fundamental obstacles to any centralized verification system,” one observer noted. “Deep packet inspection cannot function against properly encrypted traffic, and governments cannot ban TLS encryption without dismantling essential internet infrastructure.”
Proponents of verification cite child safety concerns, particularly around child sexual abuse material. “Online identification is the only way forward,” one commentator argued, pointing to the problem of automated bots and manipulative actors flooding digital spaces. “When nine out of ten internet users are actually language models, you’re being manipulated by various interests.”
However, technical experts counter that even authoritarian regimes with substantial resources struggle to enforce complete blockades. Researchers in Russia and China have documented how citizens continuously adapt circumvention techniques when detection methods improve.
“The infrastructure required for a European-style internet firewall is nearly impossible,” according to an observer familiar with network engineering. “Europe consists of competing nations without unified infrastructure. Any enforcement would require cooperation across dozens of independent governments and telecoms.”
Alternative technologies, including decentralized networks, open-source proxies, cryptocurrency payments, and packet-masking protocols, provide potential workarounds. One source described a masking technique that disguises proxy traffic as standard HTTPS to dummy websites, evading detection by manual or automated inspection.
The economic cost also weighs against enforcement. Users would bear expenses for expanded network verification infrastructure, and widespread adoption would require processing resources at unprecedented scale.
Security advocates emphasize that practical technical solutions exist for those motivated to find them, though large-scale public access remains dependent on the viability of mainstream services and infrastructure. The outcome likely hinges not on technological capability, but on whether governments can coordinate policy across competing interests.
← Back to home


Comments
Loading comments…
Leave a comment
Your name and masked IP address will be publicly visible.